Freedoor2.4.6.8 is one of those programs that people search for when they need a simple way to open blocked websites, route traffic through different paths, or experiment with privacy tools outside mainstream platforms. Yet the moment you begin researching it, you immediately encounter a wider problem. There is no widely recognized vendor name, no long-term development roadmap, and no central website with verified downloads or transparent documentation. As a result, anyone approaching this tool in 2025 needs to understand both how to perform a safe installation and how to evaluate the software itself before it ever touches a device.
This guide is written to meet modern safety expectations, user-first standards, and responsible technology practices. Because there is no official, verified developer source for Freedoor2.4.6.8, the article does not provide direct download links or endorse any unofficial mirrors. Instead, it explains how to evaluate unverified programs, how to install them safely if you choose to proceed, and how to protect yourself before, during, and after installation. By the end, you will understand not only how to install Freedoor2.4.6.8 but also how to build a safer approach to any unverified software in the future.
Understanding What Freedoor2.4.6.8 Claims to Be
People encounter Freedoor2.4.6.8 in different contexts. In some cases, it is described as a lightweight tool for bypassing restricted networks. In others, it appears framed vaguely as a privacy helper or “connection utility” promising smoother access to the open internet. Because there is no unified, authoritative description, users often end up guessing what they are installing. That alone is a reason to approach the program cautiously and thoughtfully.
Software with ambiguous identity characteristics carries inherent risks. When a tool has multiple conflicting descriptions, its purpose becomes unclear. When the developer does not maintain a public communication channel, update log, or clear security policy, you cannot evaluate the trustworthiness of the program. And when third-party blogs repeat identical installation instructions without revealing where they sourced the files, that pattern usually signals scaled content rather than genuinely vetted recommendations.
This context matters because installing a program is not a neutral action. When you run an installer, you grant it high-level access to your system, your files, and your network. Any application that manipulates network traffic, encrypts data, or interacts with restricted pathways demands an even higher threshold of scrutiny. Therefore, the safest and most sensible approach is learning how to evaluate the software before installation instead of rushing directly toward the setup process.
The First Step: Evaluating the Legitimacy of the Software
Before attempting to install Freedoor2.4.6.8, it is important to understand the difference between verified software and unverified tools. Verified software comes from a known developer, includes a changelog, offers customer or community support, and has clear documentation describing its functions. Unverified software, by contrast, often appears only on scattered blogs, mirrors, or file-sharing pages without any clear statement about authorship or maintenance.
For Freedoor2.4.6.8, the fragmented information online leaves many users wondering whether the tool is legitimate, outdated, abandoned, or even potentially harmful. While some programs with niche communities exist entirely outside mainstream distribution channels, they normally still maintain transparent communication. When that transparency is missing, the user must handle the situation with caution.
If you still decide to seek out the program, it is vital to locate a source that appears stable and minimally trustworthy. That means looking for a page that does not redirect multiple times, does not display disguised ads, and does not attempt to bundle several installers together. The safest practice is to download only a single, clean installer file without additional packages attached.
However, even if you locate what appears to be a clean file, downloading it does not mean you should execute it immediately. The evaluation process continues before the installation stage begins.
Preparing Your System Before Installation
Installing any unverified tool, including Freedoor2.4.6.8, requires several safety preparations. These steps protect you in case the program is outdated, poorly maintained, or malicious.
Begin by ensuring that your operating system is fully updated. Modern operating systems include built-in security layers that identify unsafe behaviors, block harmful processes, and alert you when a program attempts to execute suspicious actions. An outdated system lacks these protections and becomes more vulnerable to exploitation.
Next, confirm that your device has functioning security software. This can be built-in protection on Windows or macOS, or a reputable third-party tool. What matters is that your antivirus or security suite is active, updated, and capable of scanning files both on-demand and in real time. Running a full system scan before installation helps ensure that no existing threats interfere with the process.
You should also create a backup of important files. Backups protect you from accidental damage, corrupted installations, or unexpected conflicts with system components. A simple cloud backup, external drive, or offline storage medium will ensure that your data remains safe regardless of the installation outcome.
Finally, make sure you understand the basics of restoring your system. If something goes wrong, you want the ability to roll back changes quickly. That could mean knowing how to use a restore point on Windows, Time Machine on macOS, or system snapshots on Linux distributions. Although most installations finish normally, being prepared puts you in control rather than leaving your device vulnerable.
Running a Safety Scan on the Installer
Once you have a downloadable installer for Freedoor2.4.6.8, you should not run it immediately. Instead, begin by scanning the file. Open your antivirus or security program and perform an explicit scan of the installer. Even if your operating system includes automatic scanning, a manual scan adds another layer of certainty.
If your antivirus flags the file, do not ignore the warning. Even if blogs or discussion threads claim that the program is clean, your security tool’s assessment should take priority. Security systems analyze behavior patterns, digital signatures, and known threat profiles more accurately than human guesswork.
If the file passes the scan but still displays no verifiable signature or identifiable publisher, you should consider whether installation is worth the risk. Some older or niche tools lack signatures purely because they were created before signing became common. Others may be unsigned because they were never professionally developed, leaving users exposed. This uncertainty is why preparing your system beforehand is essential.
If the installer appears clean, controlled, and unmodified, you may continue to the installation phase. However, continue to monitor your system carefully and remain alert for anything unusual.
Installing Freedoor2.4.6.8 on Windows
Most users attempting to install Freedoor2.4.6.8 do so on Windows. If you choose to proceed, the installation process usually resembles that of other lightweight utilities.
Begin by right-clicking the installer and choosing whether to run it normally or with administrator privileges. Running as administrator should be reserved for software that genuinely requires elevated permissions. If the installer requests administrator access without a clear justification, reconsider installing it.
During the setup process, read every screen carefully. Many unofficial installers attempt to add optional components, browser extensions, or promotional tools that you do not want. Uncheck anything that looks unrelated. If the installer tries to force additional software without giving you an option to decline, that is a strong sign you should stop immediately.
After installation completes, restart your system if prompted. Some programs require a restart to finish writing system data or establishing network configurations. If the installer does not request a restart, consider rebooting anyway to ensure all processes initialize correctly.
Once the application is installed, examine how it behaves. Check the task manager to see what processes are active. Observe whether your system runs normally, whether any unexpected notifications appear, and whether your network behaves as expected. Suspicious behavior includes unusual CPU spikes, unexplained network traffic, browser changes, or constant background activity.
If the program behaves normally, you may begin exploring its functions. If anything appears out of place, uninstall the tool promptly and perform a security scan.
Installing Freedoor2.4.6.8 on macOS
Some users attempt to install Freedoor2.4.6.8 on macOS through a disk image or installer package. macOS includes strict security controls, so your installation process will depend on whether the file has a recognizable signature.
When you open the file, macOS may warn that the developer cannot be identified. This message is common for niche or unsigned applications, but you should treat it seriously. Overriding macOS security should be done only when you trust the developer completely. Because Freedoor2.4.6.8 lacks clear developer information, overriding security prompts may not be in your best interest.
If you proceed, open the file through System Settings by approving it manually. Drag the application into your Applications folder or follow the installation wizard provided. After installation, monitor the program’s behavior. Check Activity Monitor to see whether it runs background processes, uses unexpected network routes, or consumes excessive resources.
If macOS refuses to open the application even after approval, treat that as a protective barrier rather than an inconvenience. Tools that conflict with macOS security controls are rarely worth the potential risk.
Installing Freedoor2.4.6.8 on Linux
Linux users often believe they are safer by default, but this confidence can lead to overlooking risks. Installing unverified software on Linux can compromise your system as easily as on any other platform.
If Freedoor2.4.6.8 is available as a compressed archive or a standalone binary, extract it into a separate folder rather than placing it directly in system directories. Avoid running unknown binaries with root privileges. If the tool requires network manipulation, it may ask for elevated access, but you should grant this only after understanding how the software works.
Check file permissions before execution. Make the binary executable manually, then run it from a terminal so you can observe messages, errors, or warnings. After running the program, use system monitoring tools to check for unexpected resource usage. If you see unexplained background activity or persistent processes, remove the program and clean up associated files.
Linux installations often feel more technical, but the principles remain the same. Transparency, control, and careful monitoring are the keys to safety.
What to Do After Installation
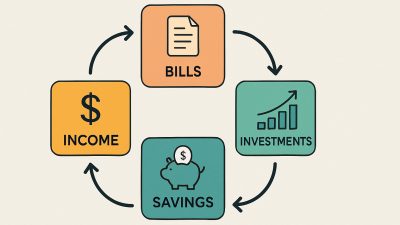
Once Freedoor2.4.6.8 is installed, your responsibility does not end. Post-installation monitoring is just as important as safe downloading and careful setup. Begin by observing how your system behaves during normal use. If you encounter slowdowns, connection irregularities, unusual pop-ups, or intrusive permissions, those are signs the program may not be trustworthy.
Check whether new startup entries have been added. Many unverified tools attempt to run automatically each time the system turns on. If this behavior is not necessary for your usage, disable it. Also review your browsers to ensure no new add-ons appeared without your consent.
Continue running periodic scans with your antivirus software. Threats sometimes reveal themselves only after the program attempts to perform certain actions. If your security tool eventually flags Freedoor2.4.6.8, uninstall it immediately even if the program previously appeared safe.
Should You Install Freedoor2.4.6.8 at All?
The question of whether you should install this software depends on your risk tolerance, your technical knowledge, and your ability to evaluate unverified applications. If you are comfortable analyzing processes, checking network behavior, and maintaining system hygiene, you might be able to use the tool cautiously.
However, if you prefer software with clear documentation, stable maintenance, and identifiable developers, this program may not be the right fit for you. Tools in the privacy or network category should ideally come from transparent and reputable sources. When transparency is missing, risk increases.
If your goal is simply to access blocked content, protect your privacy, or experiment with network routing, consider whether more established alternatives exist. The digital ecosystem includes numerous open-source programs with documented code, active communities, and clearly defined behaviors. Choosing tools with known reputations reduces the guesswork and lowers the risk of encountering unwanted software behaviors.
Read Also: USDT, Travelers, and the New Way People Move Money Into Nigeria
Final Thoughts
Installing Freedoor2.4.6.8 is not like installing a mainstream application. The lack of verified developer information, centralized distribution, and clear documentation introduces uncertainty. That does not automatically mean the tool is harmful, but it does mean the user must proceed with greater care.
The most important thing you can do is follow a disciplined safety process: evaluate the source, prepare your system, scan the installer, monitor the application, and remain aware of any unexpected behavior. Whether you ultimately decide to use Freedoor2.4.6.8 or choose a more transparent alternative, approaching unverified software cautiously is one of the most valuable digital habits you can develop.